- Home
- :
- All Communities
- :
- Products
- :
- ArcGIS StoryMaps
- :
- Classic Esri Story Maps Questions
- :
- Re: Can't display Locate Button on Story Map Tour
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am not able to bring the 'Locate' button on my map. I am using the AGOL hosted template "Story Map Tour".
Confirming the choice "Display a 'Locate' button" in Settings/Layout in builder mode does not work. I see this function important for mobile users.
I am using iPhone iOS 10.2, on desktop Firefox 50.1.0, Chrome 55.0, IE 11.
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
First check to make sure the URL to your story starts with "https." If the URL starts with "http," you are loading you story on an insecure connection. Modern browsers will not provide a user's location to a website unless the website connects using a secure connection to prevent a hacker from stealing that user's location information. Because of this, we disable the locate button when the story is loaded of "http." If you still have issues, let us know. Also, if you have a public link to your story, that will help us investigate if there is a bug in the app.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
First check to make sure the URL to your story starts with "https." If the URL starts with "http," you are loading you story on an insecure connection. Modern browsers will not provide a user's location to a website unless the website connects using a secure connection to prevent a hacker from stealing that user's location information. Because of this, we disable the locate button when the story is loaded of "http." If you still have issues, let us know. Also, if you have a public link to your story, that will help us investigate if there is a bug in the app.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you very much Stephen. This is the solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Stephen,
locate button in https works well with my map tour:
https://sit-rimini.maps.arcgis.com/apps/MapTour/index.html?appid=0a35548e898b427d86844ec07f3fc9cb
but if I plug it in to a map series does not work
https://sit-rimini.maps.arcgis.com/apps/MapSeries/index.html?appid=863b7fc94fec48fd80ce05d1b8f03b6b
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unfortunately, the locate button cannot be displayed when the map tour is embedded. This is because we never want a viewer to see a Story Map that has a locate button that will always return an error. When an story map is embedded in another page, there is no reliable way for our application to determine if the top-level webpage, and all nested pages have a secure connection (https). If at any point, the secure connection is broken, the browser will reject our request for location due to security reason. For this reason, we disable the locate button when the app is embedded.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you Stephen,
in the same map series there is also a map built with the web app builder (mappa strutture ricettive) and the locate button here works. So the safety speech only applies to the story maps?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In all cases most modern browsers will reject an app's request for location if there are any insecure scripts or iframes loaded on the page. Internet Explorer and some older versions of other browsers will still provide the location to an app even though it is a security vulnerability.
In your case the web app builder will work in every browser except the latest version of Safari (Safari, added more rules that requires all content to be requested over https, including images) because their is a secure connection for all scripts and iframe. However, as I mentioned, there is not a reliable way for apps to determine if their connection is secure and then display the button in only these cases.
The Story Maps team has decided to take a stronger approach to determine when we display the locate button. Because many viewers of story map apps are the general public we try to make our apps as simple to use as possible. We have chosen not to show the locate button to users if they will constantly get a error message that their location cannot be determined. Even if they double check their device location permissions they will still always see this message which leads to confusion. Also, we want to follow security best practices even if an older browser leaves this vulnerability open to attack. Especially because a public user has a higher likelihood that they are accessing the story from a public wifi hotspot where these attack are more likely to occur.
One other note, I looked at your story and it appears a couple of your tabs have private content in them that requires a login. Make sure to test the public version of your app from a browser you don't typically use and when you are logged out of your arcgis online account. Unfortunately, private content that requires a login from ArcGIS Online and many other services will not allow their sign-in page to be embedded and the app will not load. This is security vulnerability because the parent page or other scripts may try to steal the user's credential. It may look like it's working for you because if you are still logged into a service the embedded app can authenticate with a browser cookie instead of redirecting to a login page.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
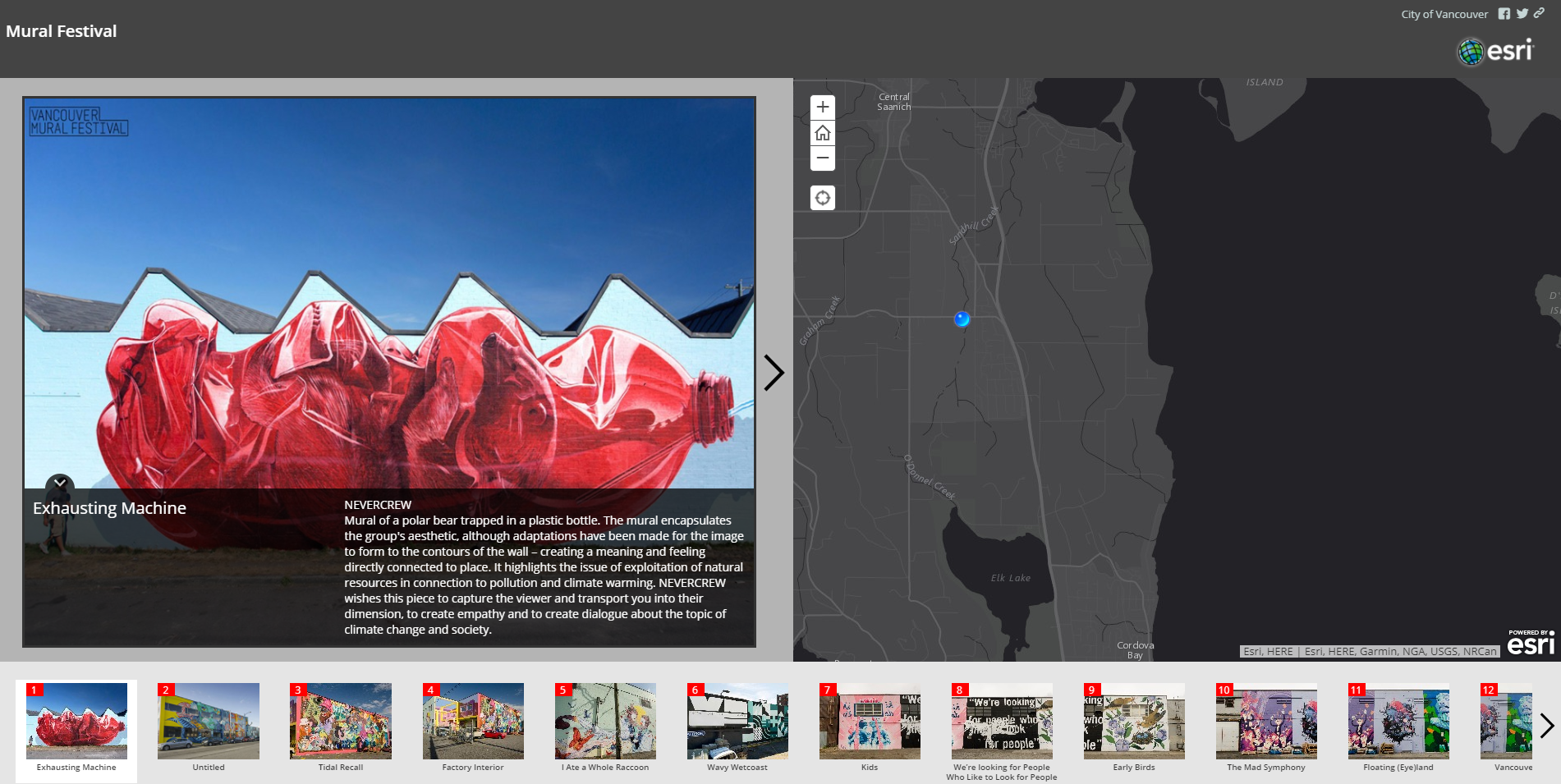
I was having similar problems but the https fixed it. However, I am receiving anecdotal reports that the geolocation is way off on iOS devices. I have tested and it is true. My physical location is at Keating.
It looks fine in desktop browser