- Home
- :
- All Communities
- :
- Developers
- :
- ArcGIS API for Python
- :
- ArcGIS API for Python Questions
- :
- Using Active Directory and Portal Tier Authenticat...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Using Active Directory and Portal Tier Authentication
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
We have Portal 10.6.1 federated with our ArcGIS Server, and have our Active Directory configured to use as logins with Portal.
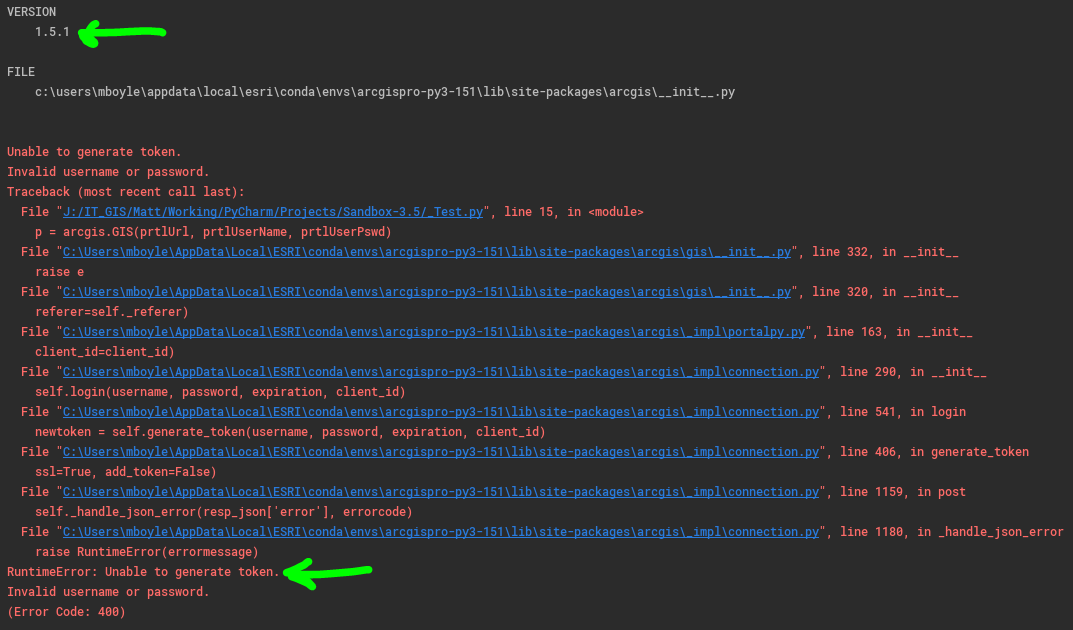
We have no issues logging into Portal, Pro, or Server Manager using our AD accounts. However, if we try to use our AD accounts with ArcGIS API for Python we continually get an error. We have upgraded to the latest ArcGIS API for Python at the time of writing this (1.5.1).
Is this a known defect...?...or is there some configuration to our Portal we need to do?
The syntax I'm using is:
arcgis.GIS('PortalURL', 'linncnty\\mboyle', 'ADPassword')Below is a screenshot of the error we get, failing to generate a token.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
does it still work using the built-in portal admin user account?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Yes ... using the initial admin account works as expected.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Hi Matthew Boyle, were you able to figure this out?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Pretty sure it has to do with the security store config in Portal Admin:
https://webadaptorhost.domain.com/webadaptorname/portaladminFrom there you'd go to: Security > Config...and if I'm wrong, someone please correct me...
By default, Portal uses a built-in store for both users and groups (named accounts). I feel pretty confident that if we were to change this to use our Active Directory, using my domain account would work.
We have kept it as a built-in user store as we may have outside organizations requesting access to web maps, services, etc... We have configured a SAML login using our Active Directory (Portal Home > Organization > Edit Settings > Security > Enterprise Logins via SAML), so this hybrid approach works well for us, where our County employees can use their domain accounts, and any outside user would be a named account.
If you want to change the security config of Portal, this link will provide you with examples on how to do that.
Keep in mind, if you are using a domain account, or the like, you'll probably want your IT to setup an account with a password that does NOT expire.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Thanks for the quick and thorough reply!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
I've never been able to get this to function correctly, even though it is supposed to be possible. Not using Portal though, but ArcGIS Online with enterprise logins. Would be curious to know if this was ever resolved. As a workaround I've resorted to using non-enterprise logins for my scripts.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
I haven't tried using it in a script like you but found that I can't generate a token with my enterprise AD account so that I could log into the server admin directory. I'm using Enterprise 10.7, two webadapters installed, federated Server with Portal and AD with Portal. I can login with my domain account and get into portaladmin, server manager, and of course portal, but can't get into the server admin directory using my domain account to get a token. i tried updating the identity store in portaladmin to windows for users, which tested fine, but still no luck generating a token.
After calling ESRI support and talking with the rep for a couple days I was told it is simply not possible to get a token using an enterprise account. I find that hard to believe, but if true I think it qualifies as a bug, something that should be fixed.
After all it states in the on the support page for setting up AD with portal that you can remove the initial builtin account after federating portal with AD.
Tip:
It's recommended that you designate at least one enterprise account as an administrator of your portal and demote or delete the initial administrator account. It is also recommended that you disable the Create an account button and sign-up page (signup.html) in the portal website so people cannot create their own accounts. For full instructions, see Configuring a SAML-compliant identity provider with your portal.