- Home
- :
- All Communities
- :
- Products
- :
- ArcGIS Web AppBuilder
- :
- ArcGIS Web AppBuilder Questions
- :
- Use of eval() function in ESRI codebase
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Use of eval() function in ESRI codebase
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
We have just had a web app fail due to a syntax error that was caused by the returned value of the eval() function. See this document for reasons not to use eval(). I've replaced this function with JSON.parse() and this has gotten our web app running again. Can anyone tell me why ESRI is using eval() in their code when it is known to cause problems?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Andrew,
I have not seen esri use the eval() function in their code. Can you provide a location where you see them using it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
They have used it in init.js located in the root of a web app that we created with Web AppBuilder from our on-premise Enterprise Portal 10.5. There is a setLocale() function at line 208, then at line 217 within this function they have this:
var userObj = eval('(' + unescape(allCookies.esri_auth) + ')');- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Hi. This is still an issue for us. Has anyone experienced this on an external facing portal serving a WAB app? Randall Williams Is the use of eval() a potential security issue?
Here's the error that the Eval() ends up producing on the client when the app is served from our external server.

Here's a screenshot of Chrome Dev Tools showing the code that is being served to the client externally when init.js contains the eval() function.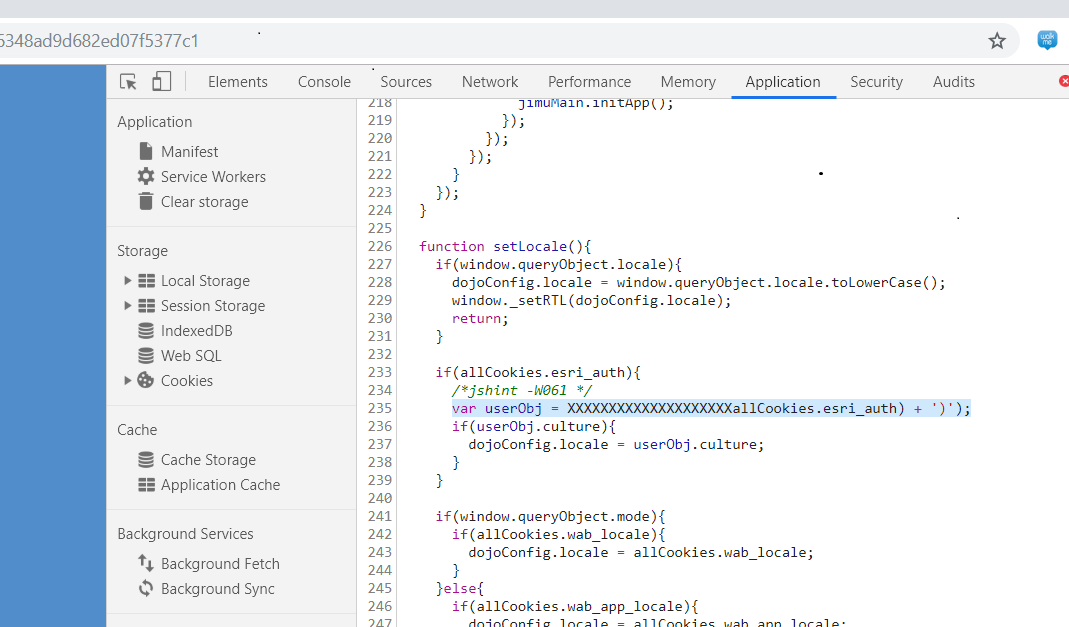
This is what we see when served internally. And there is no error.

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
This is related to:
[#BUG-000121479 Web AppBuilder Apps Require 'unsafe-inline' and 'unsafe-eval' in ContentSecurityPolicy Header]
There are issues in both the WAB and in JS API 3.x that result in breaking changes when we prevent unsafe-eval. These issues are caused in part by upstream dependencies.
My understanding is that this is addressed in the next version of the WAB (The "Experienec Builder") which shoud be out later this year.