- Home
- :
- All Communities
- :
- Products
- :
- ArcGIS Enterprise
- :
- ArcGIS Enterprise Questions
- :
- Hosting server grayed out unable to select Hosting...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Hosting server grayed out unable to select Hosting server
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
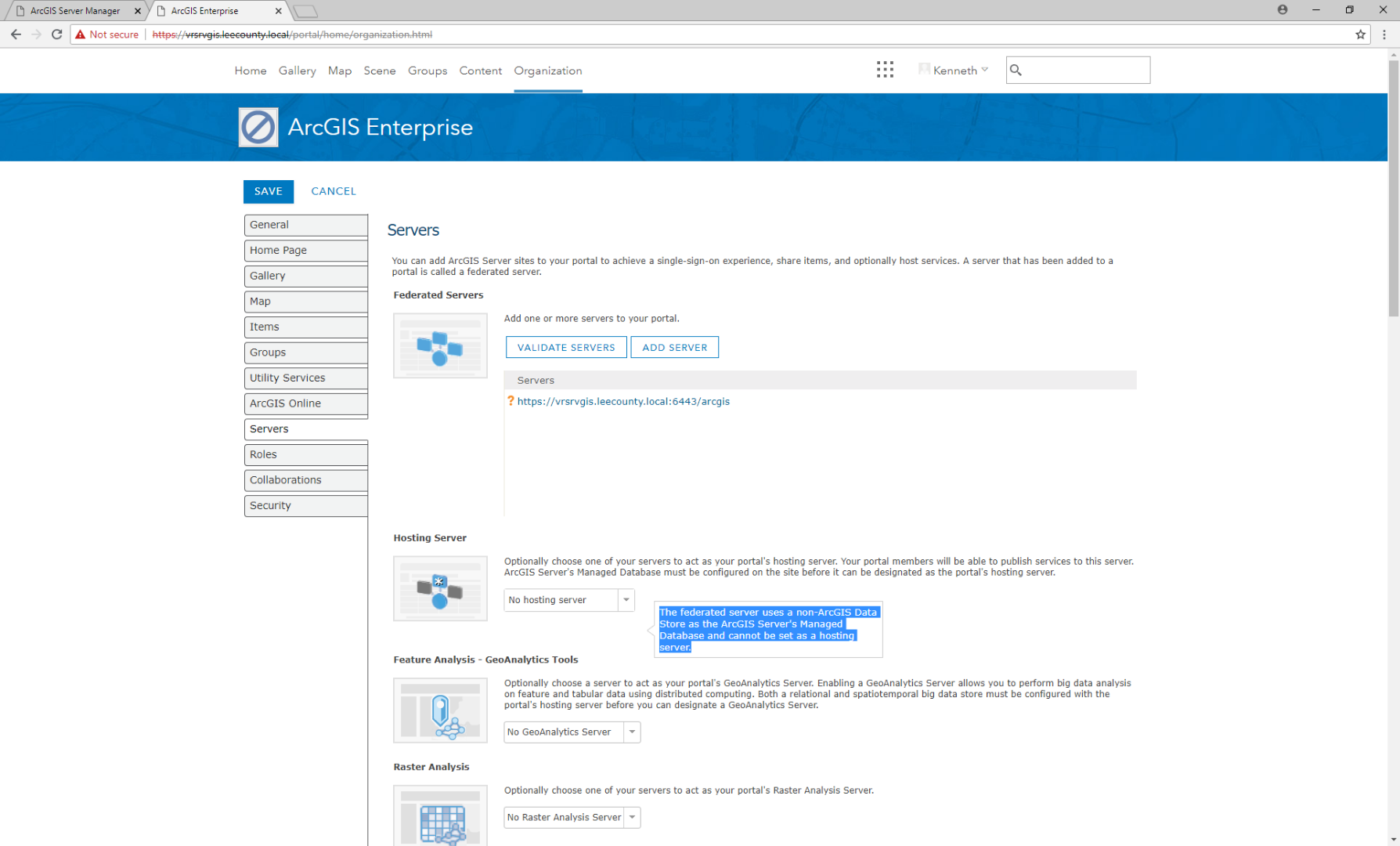
The following message is in a flyout when I put my cursor over the server.
"The federated server uses a non-ArcGIS Data Store as the ArcGIS Server's Managed Database and cannot be set as a hosting server."
I have installed Arcgis Data Store and followed the instructions but it is not showing up.
anyone have this issue?
ArcGIS_DataStore_Windows_1061_163980
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
I think this may be caused by an SSL certificate trust issue. I'd recommend checking the certificate used by Server over 6443. If this is a certificate that was imported into Server, can you confirm that Portal trusts the certificate authority that signed the certificate? If this is the default self-signed certificate that was generated when Server was installed, can you confirm that the hostname listed in the Server admin url matches the common name for the certificate? Another good way to test if Portal trusts the certificate is to use the checkUrl.jsp endpoint.
If this comes back with an http 200 response, the certificate is trusted. If this comes back with an error, it is likely a certificate issue.
Once the certificate is trusted, the Hosting Server should not be grayed out.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Did you configure the ArcGIS Data store as a relational data-store with ArcGIS Server?
Do you have any enterprise database that is configured as managed database with the ArcGIS Server?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Kenneth, did you every get this figured out?
I'm having the same issue and yes, my site has a trusted SSL, and yes, the data store has been configured as a relational and no, I do not have an enterprise DB set up as a managed DB with ArcGIS Server. Mine is a fresh install. Any help would be greatly appreciated. Kenneth, did you every get this figured out?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Check the network requests when loading the My Organization page. If you see a request from Portal to the Admin API of Server through the Admin URL you used to federate failing with a 403 error, then the problem is that the Portal doesn't trust the certificate used for the Admin URL as Jeff Smith mentioned. The Portal is attempting to determine if the Server has a registered relational Data Store and if that request fails, the option will be disabled. The Portal logs would also contain an error about a certification path not being trusted.
If all requests return a 200, then you may have to look at the response of the request I mentioned above to check what's returned.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Thank you for your quick response. I did the network request lookup and I am getting an error. A 500 error. I also checked the logs and I am receiving a Invalid SSL certificate found. PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
The funny thing, both the Portal and Server are on the same machine and I have both of them using the same imported CA SSL Cert. IIS has it binded to 443, I have imported the .pfx to both Portal and Server Apps, and pointed both apps to this imported PFX. Both Portal and Server, when browsing to the web adaptor URL, show that they are trusted.
Any ideas? What I'm I missing?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Here's an update... I went to Portal admin > Federation > Servers > Server ID > Update > Set the server as hosting server from the Server role drop-down menu. This seemed to have done the trick. Curious if this is a bug?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
There's more logic within the home application/My Organization page to ensure that you have a relational Data Store, which is the request from Portal to the Admin API to get the list of registered Data Stores. You're bypassing that logic by updating the federated Server manually, so it's not a bug.
Did you import the certificate into Portaladmin through the Import Root or Intermediate Certificate operation?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
I used the option "Import Existing Server Certificate" because I thought it was an existing since I had already exported from IIS. Do I need to remove this and import it as "Import Root or Intermediate"? I did this for both Portal and Server so I'm guessing I will need to do it there too.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
The Import Existing Server Certificate option is used if you want to use your own certificate for the 6443 and 7443 endpoints for Server and Portal. The Import Root or Intermediate operation is used to tell Portal to trust certificates. You don't need to remove anything, just import your certificate using the Import Root or Intermediate operation. If you want to use the same alias, you'll need to remove any existing certificates first.