- Home
- :
- All Communities
- :
- Products
- :
- ArcGIS Enterprise
- :
- ArcGIS Enterprise Portal Questions
- :
- SAML Certificates Installation
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
SAML Certificates Installation
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Hi All,
We have an ArcGIS Enterprise installation on AWS Ec2 machines. We are currently configuring SAML based single sign-on and IDP has provided a pubic and private key. I want to know the process of setting up Private+Public keys for SAML in ArcGIS.
There are videos available for SSL certificates configuration but they don't talk about keys configuration for SAML especially how to import the private keys (.pfx) files.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Hello,
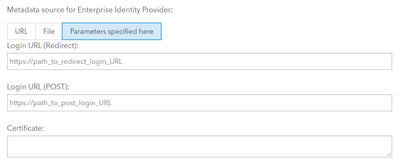
The configuration of SAML is done through the following options:
1. Using the IDP metadata url
2. Using a metadata file
3. Using parameters
The first 2 options should automatically import the correct certificate key. Sometimes that certificate is out of date or wrong, so you can manually update it by editing the SAML configuration.
The last option will allow you to specify the certificate key directly.
In my experience it is much easier (and foolproof) to use an IDP metadata url or file, as this will automatically populate everything for you.
Once you the identity provider metadata is downloaded you will then need to create the service provider metadata file and give that back to IT so they can configure the trust relationship on the IDP.
Mark
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Thanks,
We have used the parameters option and manually copied the certificate from IDP metadata file (there was some an error coming when importing the metadata file)
Now, there is another public and private key (combination of .cer & .pfx files) that is different from IDP provided one. That is our own (CA provided) public and private key. We have to provide the public cert to the IDP. Question is how do I install/update these certificates on the portal machines. I need steps required to import the SAML certs and where to store/install the private key?
Path of Portal admin directory looks like this
Home > Machines > 10.1.1.22 > SSLCertificates
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
Portal for ArcGIS uses the alias 'samlcert' to define which keypair is used for encryption/decryption of the assertion or signing of the SAML request. The steps are listed in the documentation, but essentially you delete the 'samlcert' certificate that was shipped with the product, then import a new certificate using the same alias. In a high availability Portal for ArcGIS site, you'll need to use the same certificate for both machines.
"The Encrypt Assertion and Enable signed request settings use the certificate samlcert in the portal keystore. To use a new certificate, delete the samlcert certificate, create a certificate with the same alias (samlcert) following the steps in Import a certificate into the portal, and restart the portal."
From https://enterprise.arcgis.com/en/portal/latest/administer/windows/configure-adfs.htm
-- Chris Pawlyszyn
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
We have changed the Idp for our SAML configuration. The samlcert is present in the portaladmin site under SSLCertificates and shows it is valid from a date (a year ago when we first configured SAML) well before this SAML change.
The SAML log in is working for people internal to our organization's network, but not external. Could this be due to our SAMLcert not being updated?
Do I need to delete the SAMLcert and re-create it?
If so, which certificate is supposed to be imported?
Any insight is appreciated.
Veteran, MS, GISP, Security +