- Home
- :
- All Communities
- :
- Products
- :
- Esri Software Security & Privacy
- :
- Esri Software Security & Privacy Blog
- :
- ArcGIS Online TLS Changes: Alternative Testing Met...
ArcGIS Online TLS Changes: Alternative Testing Methods – Mobile Edition
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
In the last blog I wrote, I described ways to test desktop apps, operating systems, and Java installs to validate they were correctly sending requests to ArcGIS Online in order to validate that your apps will continue to function after TLS 1.0 and 1.1 are no longer supported after April 16, 2019.
Some users have expressed concern related to their mobile apps – older Android or iOS devices may not natively have support for TLS 1.2 enabled. Android fully supports TLS 1.2 starting at Android 5 (Lolipop), but custom Android apps may have enabled support for TLS 1.2 for Android 4.1.
Starting an iOS 9, Apple introduced App Transport Security, which enforces TLS 1.2 for most apps – but it’s possible that some vendors may have globally disabled or created domain exceptions for this feature.
All that’s well and good, but for the person who’s responsible for making sure apps are going to work, what does this mean? Is there a painless way that an app or device’s TLS 1.2 compatibility can be quickly validated?
Happily, the answer is yes, and just like in the last blog, we can use the Fiddler web debugging proxy to validate!
Because Fiddler won’t run natively on a mobile OS, there’s a bit of setup we need to do before we can validate.
First, go ahead and install Fiddler on a Windows machine. While there is a beta version of Fiddler for Linux, we’ll test with Windows.
Once it’s installed, we’ll need to gather some information set some options.
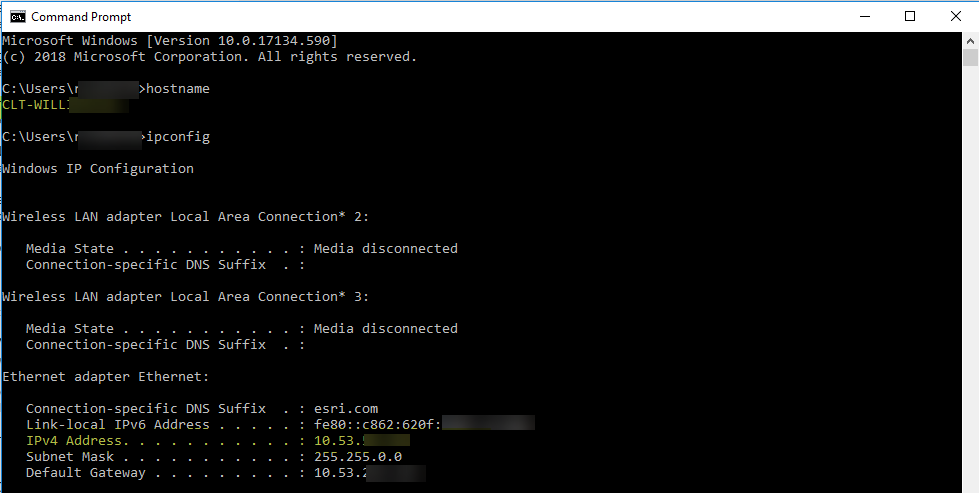
Next, if you don’t already know it, you’ll want to take note of your Windows machine hostname and IP address. You can get those details by opening a Windows console and entering the HOSTNAME and IPCONFIG commands like in the example below (details redacted to protect the innocent). These details will be used later.
Figure 1: Ipconfig and Hostname
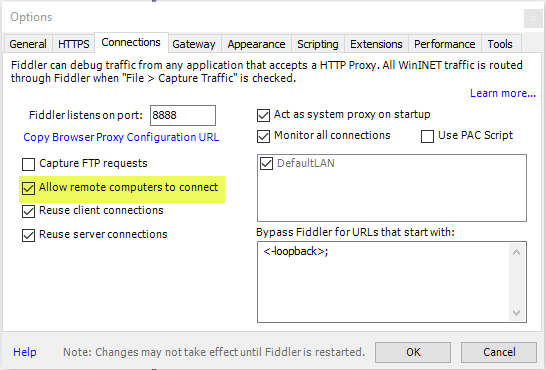
Once you have those details, open Fiddler and navigate to tools>options. Enable the option to allow remote computers to connect and keep the rest of the results.
Figure 2: Fiddler Connections options
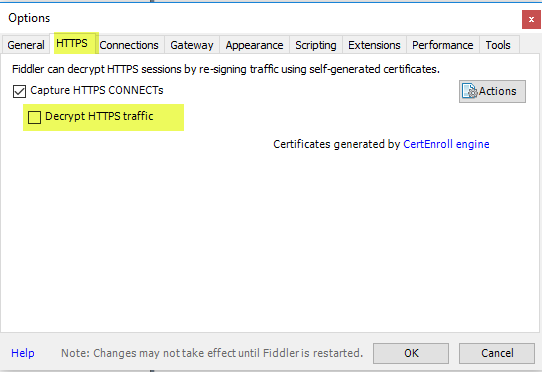
Next, click the ‘HTTPS’ tab. By default, the ‘Decrypt HTTPS traffic’ option is unchecked, but if you’ve used Fiddler to debug HTTPS traffic already, this option may be enabled.
Figure 3: Fiddler HTTPS options
Next, you’ll want to configure your mobile device to push your web traffic through the Fiddler proxy.
To do this, your mobile device will need to use WIFI and be on the same local network as your Windows machine.
I have an iOS device I’m testing with, but the instructions for configuring your device to use a proxy should be similar.
Your favorite search engine should be able to assist with specifics.
In my case, once I’ve joined the WIFI, I click on the WIFI connection and scroll down to ‘Configure Proxy’
Figure 4: WIFI proxy configuration
Once in the ‘Configure Proxy’ dialog, enable ‘Manual’ configuration, and populate the Server and Port settings.
Populate the ‘Server’ value with the hostname or IP address of the machine where Fiddler is running. By default, Fiddler listens on port 8888.
Figure 5: WIFI proxy configuration
Once that’s complete, you’re ready to test! Open your app and connect to your test resource.
Assuming your’re watching the Fiddler console, you’ll start to see your WIFI traffic being routed through the Fiddler proxy.
Click on one of the sessions that was captured that represents the endpoint you’re connecting to. In my case, I’m connecting to an internal ArcGIS Enterprise instance I maintain.
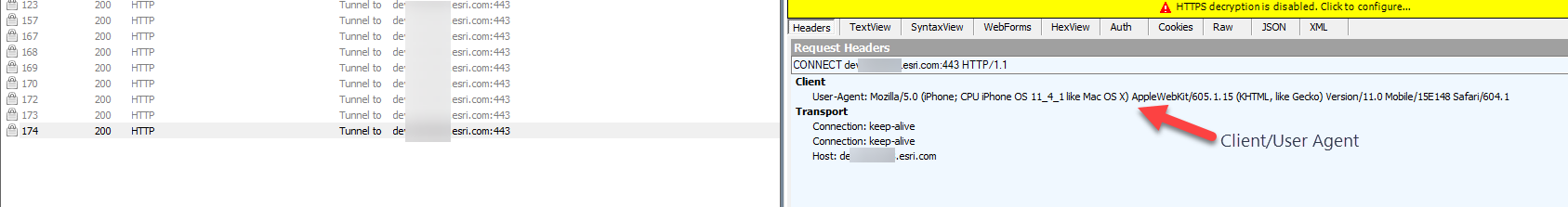
After you’ve selected a session, in Fiddler, click on the ‘Inspectors’ tab, and then the ‘Headers’ subtab. You’ll want to have a quick check to make sure that the Client is your mobile browser or app instead of a desktop browser or app. Typically Esri clients indicate “Esri” or “ArcGIS” for the user-agent.
Figure 6: Confirm user-agent in Fiddler Headers tab
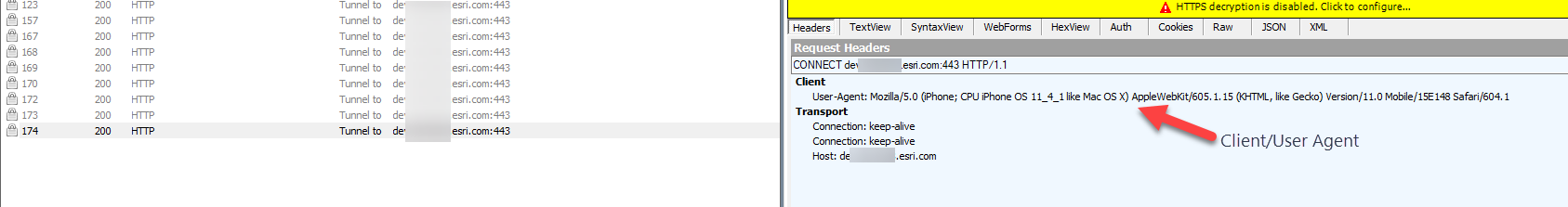
After you’ve checked the user-agent and are sure you’re reviewing the correct traffic, click the ‘TextView’ tab. Just like before, you can review the TLS version that the client is using.
Here I’m satisfied that my iOS browser is creating sessions to my server using TLS 1.2.
Figure 7: TLS version in Fiddler TextView tab
Hopefully this workflow can help users who require an additional level of validation with mobile apps they use.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.