- Home
- :
- All Communities
- :
- Developers
- :
- JavaScript Maps SDK
- :
- JavaScript Maps SDK Questions
- :
- Chrome: A cookie associated with a cross-site reso...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Chrome: A cookie associated with a cross-site resource
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In my console I am getting this warning:
"A cookie associated with a cross-site resource at http://arcgis.com/ was set without the `SameSite` attribute. A future release of Chrome will only deliver cookies with cross-site requests if they are set with `SameSite=None` and `Secure`. You can review cookies in developer tools under Application>Storage>Cookies and see more details at https://www.chromestatus.com/feature/5088147346030592 and https://www.chromestatus.com/feature/5633521622188032"
Is this something I need to adjust in my website or something that ArcGIS will prepare for?
This error also appears for my reference to OpenStreetMap and another site. All the errors in my console are a bit alarming for a junior dev!
Thanks very much!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I was just about to make a post on this myself. Starting yesterday I am also seeing the same errors. Like Rochelle, I am a bit of a novice with all of this, and am curious what steps we need to take to remedy this before Chrome makes the additional changes that they mention.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
To be clear, this is a warning only. Warnings do not equal errors. Typically, warnings will not affect your web application. Samesite is an experimental security feature added by Chrome. Please see the following 3rd party link for more information and a means to turn off the warning if you so desire:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This affects cookies sent by server-side code only, so this is something that concerns Esri. These warnings are temporary and will go away with the stable Chrome 80 release, because at that point any deprecated cookies will simply be blocked. In the meantime, if you're debugging and these warnings annoy you, you can disable them using chrome://flags ("Cookie deprecation messages").
Should client side developers be concerned? That shouldn't affect your app at all, as far as I can tell, EXCEPT for one situation: if you're developing a Chrome extension that uses chrome.cookies. If your extension's logic relies on monitoring a cookie that becomes deprecated, then you have cause for concern, but there's nothing you can do unless you're also the server-side developer (or have the developer's ear!). Then, the Stack Overflow link given above is pertinent.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm suddenly seeing this as well. Cookies default to SameSite=Lax - Chrome Platform Status and Reject insecure SameSite=None cookies - Chrome Platform Status seem to suggest this is no longer an experimental feature, and will be on by default in Chrome 80. Contrary to this FAQ: Are ArcGIS products prepared for the Chrome cross-site cookie update? , I'm seeing this on a Portal Web Map with content from an unfederated server. "...because at that point any deprecated cookies will simply be blocked", what effect will that have on users web mapping experience? Will layers simply not load? I can't imagine the cookies aren't critical for something? Panic or turn off the annoying warning?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This "feature" has been moved to defaults in Chrome 80. If you're experiencing issues, you can do the following:
1. Go into the "Chrome Flags" chrome://flags
2. Search for same
3. Disable "Enable removing SameSite=None cookies" and "Cookies without SameSite must be secure" flags
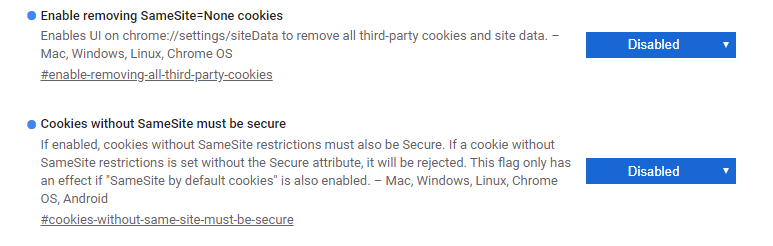
This should get you back up and running until a more complete fix can be suggested.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unfortunately that doesn't work in most organizations where GP settings prevent overriding browser security settings by the user. So my question still stands, what's going to stop working when " A future release of Chrome will only deliver cookies with cross-site requests if they are set with `SameSite=None` and `Secure`" is a reality? FAQ: Are ArcGIS products prepared for the Chrome cross-site cookie update? appears to only address AGOL, not portal or server.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey @ThomasColson @RochelleWolfe et al.,
Did you ever learn more about the state of this Chrome issue in regards to Esri Web Apps? We are seeing similar SameSite and Schemeful cookie warnings in our web apps and hear our organization will be implementing a Chrome update that makes these (previously experimental) features default / always on towards the end of January. I'm unsure right now as of the level of impact that this will actually have to users of our apps. I have tried going into the chrome://flags settings page and setting all of these (currently) experimental settings to "Enabled" and our apps appear to still load and function fine within Chrome. Thanks for any updates and info you can share!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is this still an issue to be concerned about? My application that uses JSAPI 4.x is getting the warning for the arcgis.com domain - with 285 requests affected, one for each JSAPI resource. I see that even the Samples page (https://developers.arcgis.com/javascript/latest/sample-code/) gets these warnings for google.com and go.pardot.com.
If the fix is on the server, arcgis.com has not yet implemented it, at least not for the 4.x JSAPI CDN. Is there anything I can do about it in my app configuration? (I'm not talking about suppressing the warnings with browser flags.) Should I just stop worrying about it?