- Home
- :
- All Communities
- :
- Products
- :
- ArcGIS for Office
- :
- ArcGIS for Office Questions
- :
- Re: Has anyone else seen ArcGIS Maps for Office 4....
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
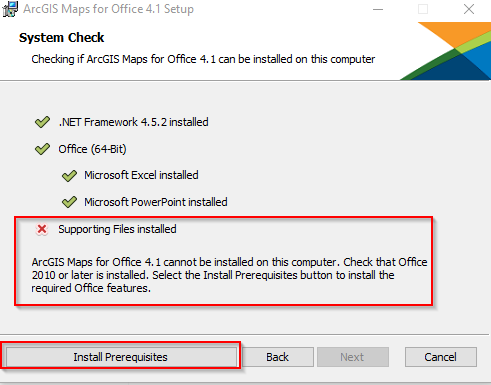
Has anyone else seen ArcGIS Maps for Office 4.1 installation executable flagging and blocked as a Virus/Malware Error during the installation on Windows 10 (1709) with 64-bit Office 2013?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
After clicking the Install Prerequisites button the installation gets blocked and halted
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There are a causes for this issue ranging from actual compromise to software security suite false positives. The following operations will help narrow down the root cause:
Validate the Binary
Use a third party technology to validate the binary as potentially compromised as well as to verify its hash value against the original binary available from Esri's website. This can be done at a number of sites such as www.virustotal.com.
1. Upload & scan the suspected binary to a site such as www.virustotal.com. We did this with the clean source file hosted by esri, the results can be viewed here: https://www.virustotal.com/#/file/a3f758644774f36dca0b05fa87781b90b2e5caf3d0942b162b2a9a5815ed2c85/d...
If the file you upload presents a different profile than seen above (eg. reports any infections at all,) immediately alert your organizations IT/Software security team if available. The binary should be destroyed, and any systems the binary was processed through should be thoroughly scanned for signs of further infection.
2. Compare the SHA256 signature of the suspected file against the actual SHA256 signature of the file hosted by Esri. The SHA256 signature of the current release (4.1) of the ArcGIS Maps for Office 64-bit installer is:
| SHA-256 | a3f758644774f36dca0b05fa87781b90b2e5caf3d0942b162b2a9a5815ed2c85 |
|---|
Again, the www.virustotal.com site will report the SHA256 hash of the file you upload for comparison. Also/Instead, you may also execute the PowerShell command: "Get-FileHash ArcGISMapsForOffice_x64_4.1_en.exe" to process and display the SHA256 hash of the ArcGIS Maps for Office installation binary for comparison.
If the SHA256 file hashes do not match, the file may be corrupt or similarly compromised. Destroy the file and download a new copy of the binary here, and proceed with installation: ArcGIS Maps for Office.
False Positive: Whitelist Binary
If the above tests confirm the SHA256 hashes match the original file hosted by Esri, and the file reports to be uncompromised then we can reasonably conclude the file is not infected and that the security software on the system is reporting a false positive *or* the security software expressly requires installation binaries be whitelisted (allowed to install.)
In this case, submit the binary to your IT/Software Security team for whitelisting action.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There are a causes for this issue ranging from actual compromise to software security suite false positives. The following operations will help narrow down the root cause:
Validate the Binary
Use a third party technology to validate the binary as potentially compromised as well as to verify its hash value against the original binary available from Esri's website. This can be done at a number of sites such as www.virustotal.com.
1. Upload & scan the suspected binary to a site such as www.virustotal.com. We did this with the clean source file hosted by esri, the results can be viewed here: https://www.virustotal.com/#/file/a3f758644774f36dca0b05fa87781b90b2e5caf3d0942b162b2a9a5815ed2c85/d...
If the file you upload presents a different profile than seen above (eg. reports any infections at all,) immediately alert your organizations IT/Software security team if available. The binary should be destroyed, and any systems the binary was processed through should be thoroughly scanned for signs of further infection.
2. Compare the SHA256 signature of the suspected file against the actual SHA256 signature of the file hosted by Esri. The SHA256 signature of the current release (4.1) of the ArcGIS Maps for Office 64-bit installer is:
| SHA-256 | a3f758644774f36dca0b05fa87781b90b2e5caf3d0942b162b2a9a5815ed2c85 |
|---|
Again, the www.virustotal.com site will report the SHA256 hash of the file you upload for comparison. Also/Instead, you may also execute the PowerShell command: "Get-FileHash ArcGISMapsForOffice_x64_4.1_en.exe" to process and display the SHA256 hash of the ArcGIS Maps for Office installation binary for comparison.
If the SHA256 file hashes do not match, the file may be corrupt or similarly compromised. Destroy the file and download a new copy of the binary here, and proceed with installation: ArcGIS Maps for Office.
False Positive: Whitelist Binary
If the above tests confirm the SHA256 hashes match the original file hosted by Esri, and the file reports to be uncompromised then we can reasonably conclude the file is not infected and that the security software on the system is reporting a false positive *or* the security software expressly requires installation binaries be whitelisted (allowed to install.)
In this case, submit the binary to your IT/Software Security team for whitelisting action.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Working with esri support to determine what the pre-req step is trying to do.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We certified the exe with our virus vendor but still get the violation error.
Tried it on another desktop – same error.
Just tried first manually installing the 2010 Tools for Office runtime and then Maps for Office installs fine.
Something about how the exe is trying to do the pre-req installs is not allowed.
Now we have a workaround.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Were you ever able to perform this software install?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Not yet, just moved my desktop from Office to Microsoft Office 365 ProPlus and are about to update Portal from 10.5.0 to 10.6.1
The Maps for Office install docs do not show Office 365 is supported.
"ArcGIS Maps for Office is available in 30 languages, works with Microsoft Office 2013 and 2016 and supports both 32-bit and 64-bit versions"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry about hijacking this thread, but besides having problems with the ArcGIS Maps for Office install, has the Virus/Malware used at your organization created any other issues with your GIS environment?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nope, not for a long-long time.
The last one I remember was when an update got applied and started deleting all the esri .exe files.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Was this occurring on both desktops and Windows Servers?
What specific Virus/Malware software does your organization use?
Were you able to resolve the problem by moving to a newer version of the Virus/Malware software?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, desktop and servers, another update was soon available that no longer tried to delete those files.
I don't remember which vendor it was. That was a few vendors ago.