- Home
- :
- All Communities
- :
- Products
- :
- ArcGIS Online
- :
- ArcGIS Online Blog
- :
- ArcGIS Blog: The Author, Contractor and some Manag...
ArcGIS Blog: The Author, Contractor and some Managers: A Tale of Roles and Privileges
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Check out this ArcGIS Blog about custom roles!
What do submarine sandwiches and ArcGIS Online have in common? They’re better with custom roles.
What a knee slapper?!? Custom roles are a helpful tool that enable administrators to fine-tune the capabilities and levels of access that their ArcGIS Online organization’s members have. ArcGIS Online has four default roles: Viewer, User, Publisher, and Administrator, which enable organization members to complete a broad set of workflows. As ArcGIS Online organizations have grown in numbers and size (there are over 995,000 organization users), the roles and methods of managing members and content have changed. Currently there are over 13,000 custom roles being used by organizations that provide users with a slightly different set of privileges than what is available through the default roles. This blog will highlight 4 custom roles and the privileges required to accomplish specific workflows in an ArcGIS Online organization.
There are two types of privileges available when configuring custom roles—general privileges and administrative privileges. General privileges allow members to perform user-based tasks like content creation, sharing and editing that are required for members to complete their work. Administrative privileges include additional capabilities to manage members, groups and content within the organization. It is important to understand what type of work each member needs to complete and assign only the appropriate privileges to enable your members to be successful. The roles below describe two common user roles for content creators with different sharing needs and two common administrative roles that enable content and member management.
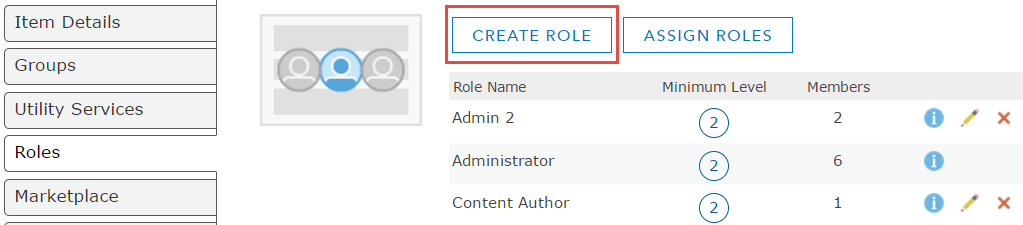
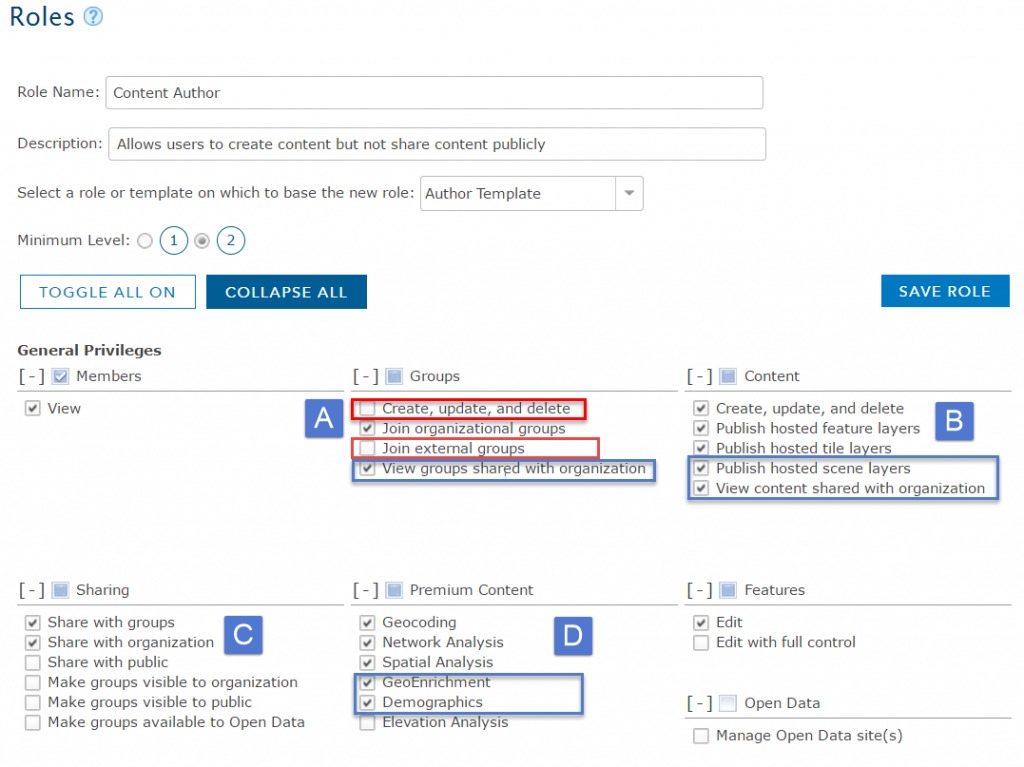
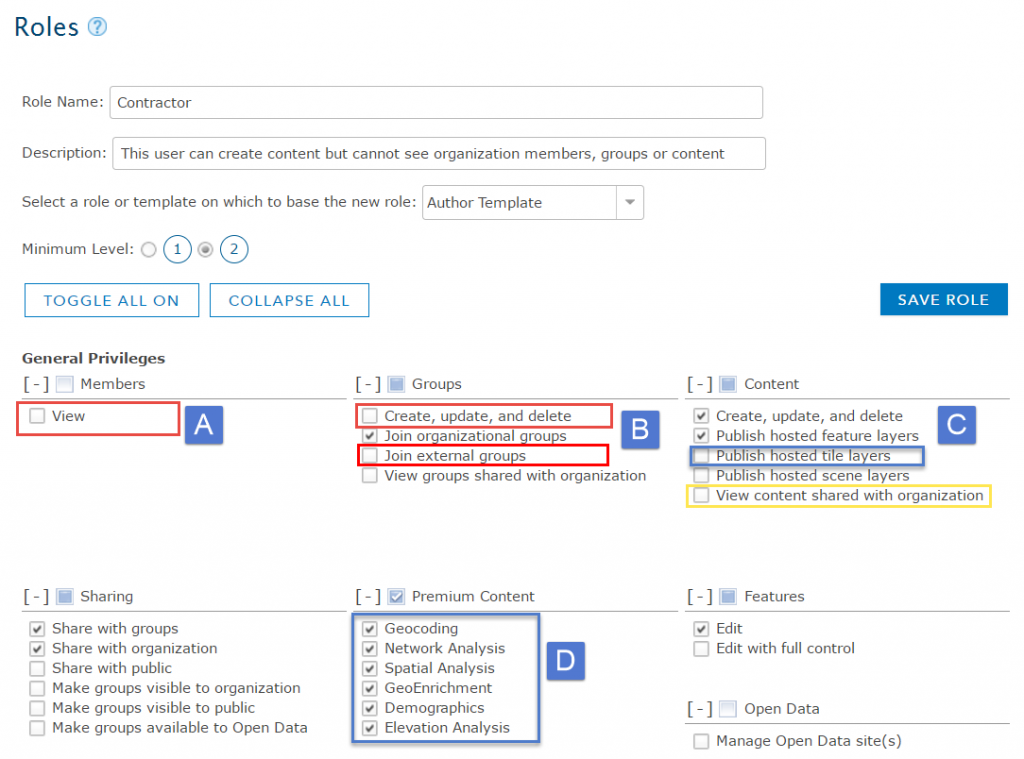
To create a custom role, navigate to My Organization and select the Edit Settings button. Click on the roles tab and click on create a role button. When setting up a custom role, select a template role or an existing role to get started. Templates are created with common privileges to accomplish a specific task. As users can have different responsibilities in each organization, creating a custom role from a template, by adding and removing privileges helps to fine tune access and capability needs for members in your organization. In the example role images, the red box indicates privileges that were disabled from the template and blue boxes indicate where additional privileges were enabled.
User Role: Content Author
A common role in ArcGIS Online organizations is a Content Author. This user is responsible for creating content for the organization such as layers, maps and apps, but is not responsible for creating and managing groups or publishing content publicly. Once the content is ready to be shared, it needs to be reviewed by a Content Manager and then shared with the appropriate audience. Often with a Content Author, there is a review and publishing process to ensure that public content is being published by an authoritative account in the organization and that all of the information product standards have been followed. (Check out this Geonet blog that outlines a sample workflow for publishing authoritative data.)
To set up a custom role for a Content Author, use the Author template as a starting point. As this user is responsible for content creation within the organization, they will not have the privilege to create groups nor join groups from other organizations but can view groups shared with the organization (A). The Content Author will be able to create all types of content (B). Under the sharing privileges this user can share with the organization and groups but will not have the capability to share content publicly (C). The Content Author will also need access to GeoEnrichment, and Demographic Services in order to create content using Esri data and include demographic map services in their maps. These privileges are enabled in addition to the default premium content for the author template (D).
User Role: Contractor
The Contractor Role would be created for temporary users whose main responsibility is also to create content for the organization. As these members aren’t necessarily an employee of the owned organization there may be content and members that should not be viewed by the contractor, but the content created (layers, maps and apps) will need to be visible and located in the owners organization.
The Author template will also be used as a starting point for the Contractor Role. The sharing, and edit privileges will remain the same as the Author Template role. The view privilege under the members tab is disabled and prevents the user from viewing the My Organization page. The contractor won’t be able to see the other members in the organization (A). They will have the ability to join groups they are invited to, but can’t create or view groups shared with the organization (B). This contractor is responsible for creating feature layers and apps, so they do not have privileges to publish hosted tile or scene layers. They are prevented from viewing content that is shared with the organization (yellow) (C). This contractor will be using the create Viewshed tool, so will need to have access to the elevation analysis service (D). This will allow the user to create content for the organization without viewing any private information.
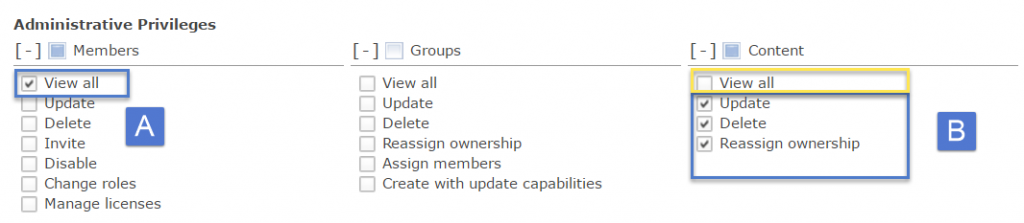
Administrative Role: Content Manager
The Content Manager is a role for a user that is responsible for reviewing and sharing content created by the Content Author and then sharing the content with the correct audience, the public for this example. The Content Manager will need some administrative privileges so they can manage other member’s content by reassigning and editing data as needed.
For the Content Manager, start with the Publisher Template which enables most general privileges. This user will need to be able to reassign content to other members in the organization. For this reason, they need the privilege to view all members (A). This user will be able to create groups using the general privileges granted through the Publisher Template. For this example role, the content manager is only responsible for reviewing the content for their department which has specifically been shared with them. For this reason, check on all of the administrative content privileges and un-check View all privilege (yellow)(C). View all content is an inherited permission and must be specifically disabled to limit the visibility of all content for this user.
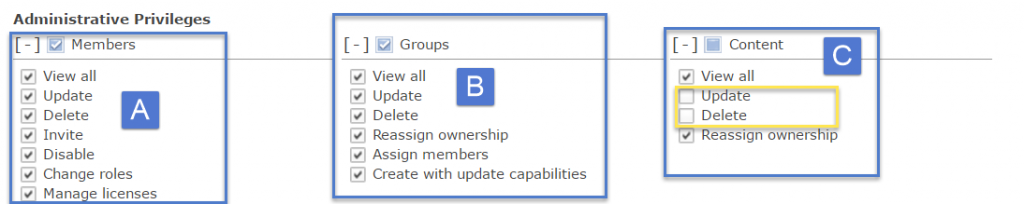
Administrative Role: Member Manager
The Member Manager is a role that provides the user with privileges to perform member specific tasks. When a new member is added to the organization, a member manager must ensure that the user is invited, assigned the correct role, licenses and is a member of the correct group. When a user leaves the organization, a member manager must remove their privileges and re-assign their content to new owners.
For this role, start with the Publisher Template and enable all of the members and groups administrative privileges. This will allow the member manager to create groups, add users to groups and delete groups (B). The member administrative privileges will enable the member to perform all tasks needed for adding and removing a user to and from an organization (A).
When a user is being removed from an organization, they can’t be assigned a license, own a group or own content. Ensuring that the member doesn’t own content is often difficult for Member Managers in deciding whether to delete or re-assign the content. This user will not be given the privileges to update or delete content as they must ensure that no data is lost when a user leaves the organization. For this reason they can only reassign content (C).
Once created, these four custom roles can be assigned to members so they can perform specific tasks as required by their job. Some of the roles also prevent users from being able to view content and perform specific tasks that aren’t required by their job. Check out the following blog to see how these roles are applied to a specific content management workflow.
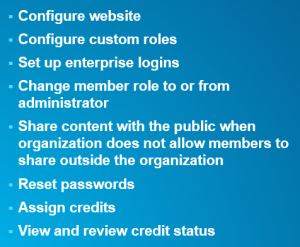
Note: The default administrator role includes a full set of privileges that can be assigned through custom roles as well as some privileges that are reserved for default Administrators only. Configuring custom roles is a reserved privilege that can only be accomplished by a default administrator. If a member requires any of the privileges in this box of reserved privileges, they will need to have a default administrator role assigned.
Helpful links:
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.